Hackers have sex video pornodiscovered a new way to remotely take control of your computer — all through the Google Chrome web browser.
A report from cybersecurity company SquareX lays out the new multifaceted cyberattack, which the firm has dubbed "browser syncjacking."
At the core of the attack is a social engineering element, as the malicious actor first must convince the user to download a Chrome extension. The Chrome extension is usually disguised as a helpful tool that can be downloaded via the official Chrome Store. It requires minimal permissions, further cementing its perceived legitimacy to the user. According to SquareX, the extension actually does usually work as advertised, in order to further disguise the source of the attack from the user.
Meanwhile, secretly in the background, the Chrome extension connects itself to a managed Google Workspace profile that the attacker has set up in advance. With the user now unknowingly signed into a managed profile, the attacker sends the user to a legitimate Google support page which is injected with modified content through the Chrome extension, telling the user they need to sync their profile.
When the user agrees to the sync, they unwittingly send all their local browser data, such as saved passwords, browsing history, and autofill information, to the hacker's managed profile. The hacker can then sign into this managed profile on their own device and access all that sensitive information.
The attack up to this point already provides the hacker with enough material to commit fraud and other illicit activities. However, browser syncjacking provides the hacker with the capability to go even further.
Using the teleconferencing platform Zoom as an example, SquareX explains that using the malicious Chrome extension, the attacker can send the victim to an official yet modified Zoom webpage that urges the user to install an update. However, the Zoom download that's provided is actually an executable file that installs a Chrome browser enrollment token from the hacker's Google Workspace.
After this occurs, the hacker then has access to additional capabilities and can gain access to the user's Google Drive, clipboard, emails, and more.
The browser syncjacking attack doesn't stop there. The hacker can take one further step in order to not just take over the victim's Chrome profile and Chrome browser, but also their entire device.
Through that same illicit download, such as the previously used Zoom update installer example, the attacker can inject a "registry entry to message native apps" by weaponizing Chrome’s Native Messaging protocol. By doing this, the attacker basically sets up a connection "between the malicious extension and the local binary." Basically, it creates a flow of information between the hacker's Chrome extension and your computer. Using this, the hacker can send commands to your device.
What can the hacker do from here? Pretty much anything they want. The attacker will have full access to the user's computer files and settings. They can create backdoors into the system. They can steal data such as passwords, cryptocurrency wallets, cookies, and more. In addition, they can track the user by controlling their webcam, take screenshots, record audio, and monitor everything input into the device.
As you can see, browser syncjacking is nearly completely unrecognizable as an attack to most users. For now, the most important thing you can do to protect yourself from such a cyberattack is to be aware of what you download and only install trusted Chrome extensions.
Topics Cybersecurity Google
 Meeting Eve Babitz by Lili Anolik
Meeting Eve Babitz by Lili Anolik
 Victor Wembanyama’s Summer League debut was NBA Twitter’s hype cycle at its silliest
Victor Wembanyama’s Summer League debut was NBA Twitter’s hype cycle at its silliest
 Was Holly Golightly Bisexual? by Rebecca Renner
Was Holly Golightly Bisexual? by Rebecca Renner
 Cibao FC vs. Guadalajara 2025 livestream: Watch Concacaf Champions Cup for free
Cibao FC vs. Guadalajara 2025 livestream: Watch Concacaf Champions Cup for free
 Colleen Ballinger allegations: What's going on with the YouTuber's ukulele song response?
Colleen Ballinger allegations: What's going on with the YouTuber's ukulele song response?
 Who should get a plus one at a wedding? The answer is tricky.
Who should get a plus one at a wedding? The answer is tricky.
 ChatGPT revealed personal data and verbatim text to researchers
ChatGPT revealed personal data and verbatim text to researchers
 Boston Celtics vs. Dallas Mavericks 2025 livestream: Watch NBA online
Boston Celtics vs. Dallas Mavericks 2025 livestream: Watch NBA online
 Muting someone on Instagram? A growing reason is envy.
Muting someone on Instagram? A growing reason is envy.
 9 Tech Products That Were Too Early to Market
9 Tech Products That Were Too Early to Market
 The cherry emoji and 14 other emoji you can use to sext
The cherry emoji and 14 other emoji you can use to sext
 Colleen Ballinger allegations: What's going on with the YouTuber's ukulele song response?
Colleen Ballinger allegations: What's going on with the YouTuber's ukulele song response?
 On The Radio, It’s Always Midnight
On The Radio, It’s Always Midnight
 Amazon CEO tries to sell kids on working on the moon
Amazon CEO tries to sell kids on working on the moon
 Why Flyana Boss's "You Wish" should be your song of the summer
Why Flyana Boss's "You Wish" should be your song of the summer
 5 fanfiction sites that aren't Archive of Our Own
5 fanfiction sites that aren't Archive of Our Own
 Paris, Reviewed
Paris, Reviewed
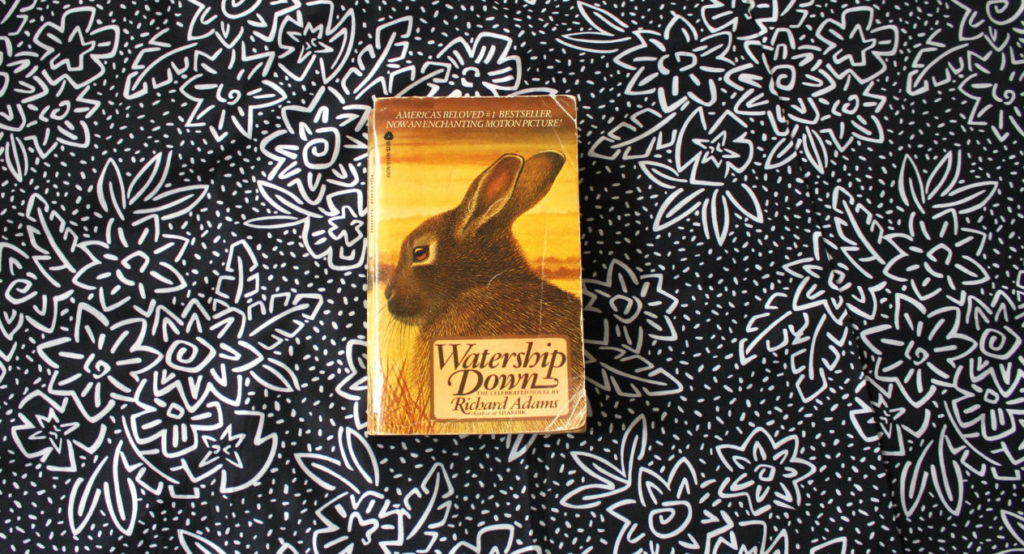 Revisited: Watership Down
Revisited: Watership Down
South Korean cosmetic brand Laneige has a new fashion collaboration and it's a hootNews host apologises for transphobic slur on Australian televisionHighlights from the Senate hearing on consumer data protectionOculus Quest hands onHow supporters of Christine Blasey Ford are showing solidarityOppo's next flagship might have an unearthly 10GB of RAMHere's how to get new Dynamic Desktop wallpapers for MojaveBlack Lives Matter mothers movingly endorse ClintonThe 'blood boy' clinic is coming to NYC so rich people can live forever'Minecraft: Dungeons' delivers a new way to play 'Minecraft' in 2019If politicians were famous Philadelphia attractionsElizabeth Banks spoofs Trump's strange entrance at the Democratic conventionRansomware attack hits Port of San DiegoSnapchat's new mission: getting you to buy more stuffDyson spent over 10 years developing the 360 eye robot vacuum. How does it rank?South Korean cosmetic brand Laneige has a new fashion collaboration and it's a hootSome basic steps to protect your Facebook account after hack hits 50 million usersBear's summer plans include napping in your backyard kiddie poolRussian hackers are taking their cyber warfare to the next levelDyson spent over 10 years developing the 360 eye robot vacuum. How does it rank? Someone's already has the iPhone X out in the wild Be your own publicist: How to use your resume to really sell yourself Hurricane Nate intensifies as it takes aim at vulnerable Gulf Coast Comfort dogs are helping people with the trauma of the Las Vegas shooting Download this: Apple Music's Facebook bot suggests songs based on emoji Say hello to Apple's new iOS 11 emoji Tesla delays semi truck debut to focus on Puerto Rico aid and Model 3 Costco will finally deliver all those giant bulk items with its new grocery service Friends don't let friends go apple picking MashReads Podcast: Getting nostalgic over hope and change with former Obama speechwriter David Litt Now that Amazon's a thing, malls have to get creative to survive Why teenage boys don't want to call themselves feminists Huge update should fix most problems of the Essential Phone's camera Season 8 of 'Game of Thrones' will begin production on Sunday A letter from the front lines of the 'Rick and Morty' McDonald's sauce war Why everyone is so convinced Facebook is spying on their conversations Sony's bringing back an old favorite to get back into AI Microsoft's Joe Belfiore just buried Windows Phone...on Twitter 'Marvel's Runaways' premieres first episode at New York Comic Con Google got permission to float its internet
1.7304s , 8612.75 kb
Copyright © 2025 Powered by 【sex video porno】,Exquisite Information Network